Trusted by over 30,000 organisations across the globe, Automate.io is the gold standard for workflow automation.
Is Automate io Safe? Automate.io utilises military-grade encryption where the users data is encrypted in rest and transit. The platform runs on Hypertext Transfer Protocol Secure (HTTPS) by where the data flow between is encrypted on both the client and the server. This method uses long-term public and private keys to generate a short-term session key.
Company’s like Adobe, Intel, Uber and Vonage trust Automate.io as a consider it safe.
Automate.io – Data, Privacy and GDPR
- All of the Automate io network communications happen on secure HTTPS protocol offering a high level of network security.
- All credentials (for the third-party apps you grant permission to), are stored in an encrypted format.
- We now have a GDPR compliant Data Processing Agreement (DPA), that our customers can optionally sign with us.
- Automate.io is Privacy Shield compliant. We comply with the EU-U.S. Privacy Shield Framework and Swiss-U.S. Privacy Shield Framework.
You can email their support if you have any specific questions relating to security for your apps as well as you should do your own due diligence to find out security elements are important to you.
Table of contents
What is Automate.io?
Automate.io is a well-designed, feature-packed integration platform that is competitively priced. Their team offers superb technical support to its clients for their Integration as a Service (IaaS) platform.
This platform was developed in 2016 by a team of developers who, albeit new to the industry, have continuously worked hard to position themselves as one of the best options when it comes to task automation.
The developers are constantly updating the platform by adding integrations and functionalities from time to time. You can review their privacy policy here.
At present, this San Francisco and India-based company has garnered more than 30,000 customers from small businesses to Fortune 500 companies that are spread all over 93 countries.
Need an automation platform?
If you are considering Automate.io, please check out our review on the platform which includes a detailed analysis of the platform and use cases for you. Check it out here.

Security Considerations for Automate io?
When reviewing any of the platforms you should understand that the provider is responsible for securing their own platform, network, applications, their own operating system (OS) and any of their own physical infrastructure.
The end user is actually responsible for securing their own customer data and any access to it. You as the end owner of your customer data need to consider the following practices that can help you protect your data in their platform.
- Audit Your Own Network – There are third party providers called Cloud Access Security Brokers that can review and audit your network for any rogue services or compromised accounts. With the advent of SaaS platforms and user becoming more comfortable with citizen development, the average company uses a surprisingly high number of third party cloud services (Okta Report 2021).
- Company Controlled User Access Management – Especially now that many workers are working from home, identity and access management (IAM) is becoming more important as a control to ensure that when a new applications is rolled out that user permissions align to what they should have access to.
- Encryption (Automate.io Covered) – As stated before Automate.io utilises double covered encryption for data at rest and in transit, therefore, it is considered safe but the end user should also consider their own data between the end user and the cloud or between other cloud applications. This can also be covered in the scope of work for a CASB.
- Apply DLP or Data Loss Prevention Monitors – Blocking malware or hackers is common place now, DLP software platforms focus on ensuring that outgoing transmissions that download sensitive data are blocked and siloed.
- IP or Collaborative Sharing of Data Monitoring – Email, team accounts and cloud storage platforms like Box or DropBox enable access points for nefarious players. User data logs and history can set predictable expectations for the systems to monitor and when use cases go outside of these experiences then the monitoring systems can enable their protection.
CASB solutions, which are typically SaaS applications, may provide additional capabilities. These may include:
- File encryption
- Pre-built policy templates to guide IT staff through the process of policy creation
- User entity behavior analytics (UEBA) backed by machine learning
- In-application coaching to help end users learn improved security practices
- Security configuration audits to suggest changes to security settings based on best practices
Four Security Accreditations/Frameworks for SaaS Providers
If you see any of these accreditations for your SaaS providers, then you know you are in good hands. Each of these frameworks or accreditations are internationally recognized and are considered trustworthy in the InfoSec industry.
- ISO 27001 – Considered the “Gold Standard” for SaaS platforms, this universally recognised accreditation is the most popular in the world. It is actually relevant to any industry and is internationally recognized.
- SOC 2 – Covering you for Security, Availability, Processing Integrity, Confidentiality, and Privacy, SOC is also an internationally recognized security audit framework for the security of your SaaS platform. These 5 trust principles will provide proof to your clients that they can trust your platform.
- OWASP ASVS – Testing and hardening your SaaS platform application is a critical element to getting a third party to trust you. The ASVS stands for Application Security Verification Standard which is an open and standardized framework for technical security controls.
- CSA STAR – Focusing on the “key principles of transparency, rigorous auditing, and harmonization of standards.” the Cloud Security Alliance (CSA) is a publicly accessible document library of companies to show current and potential customers their security and compliance posture, including the regulations, standards, and frameworks they adhere to.

Other Considerations for Security and Using Automate.io
Consider reviewing your internal processes of your company. Ask questions like do you use multi-factor authentication when signing into your SaaS apps, or do you have a tight on-boarding and off-boarding program to ensure users cannot gain access after leaving the business.
- Provide Security or Anti-Phishing Training for Employees on a Regular Basis.
- Consider Cloud-to-Cloud Back Up Solutions
- Consider a Password Management Tool such as 1Password or LastPass.
- Streamline Identity and Access Credentials Management (IAM)
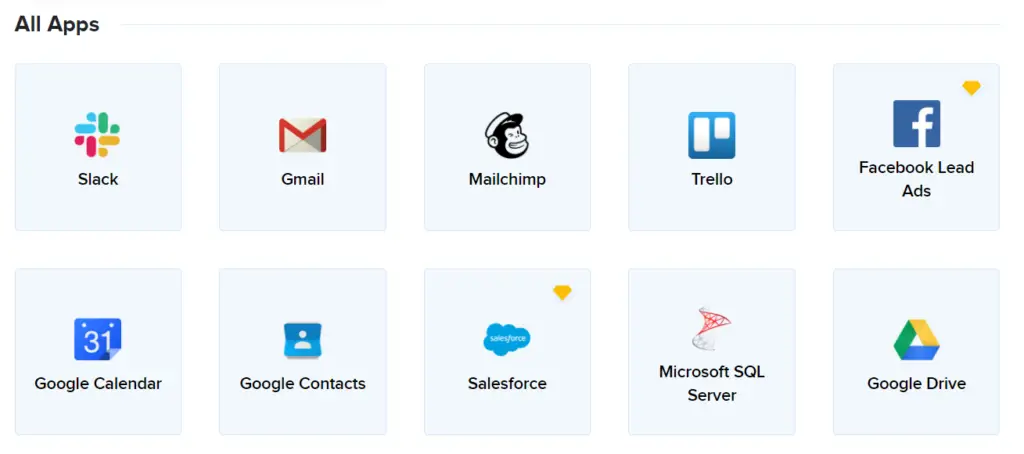
Also, consider reviewing your current integrations and platforms that you already use. Below are some examples of the most popular integrations with Autmate.io.